News broke yesterday that the city of Dallas, Texas, had been severely affected by a malicious ransomware attack. The city itself has not issued many statements about the incident, but news stations in the area have been covering the attack and resulting aftermath closely, because the attack has had far-reaching effects across Texas.
Attacks like this are always alarming for public agencies, especially public safety agencies. Attacks always carry the risk of taking down an entire network and halting critical operations.
The Ransomware Attack
According to statements from the city, their security operation center (SOC) detected an in-progress cyber attack early on Wednesday May 3. They knew about the attack before it took down their network. We can assume that once they were alerted of the attack, they took any possible measure to mitigate its effects and spread. However, we know that the network that is the backbone of their emergency response infrastructure was taken offline as a result of the ransomware attack.
According to CISA, “Ransomware is a form of malware designed to encrypt files on a device, rendering any files and the systems that rely on them unusable. Malicious actors then demand ransom in exchange for decryption.” In the case of this cybersecurity attack on the City of Dallas, it’s been reported that a group who calls themselves Royal gained access to the network, encrypted files on the network, and rendered much of it useless. The group threatens to publicly release sensitive information that was found on the network if the City doesn’t pay the ransom.
Outages City-Wide

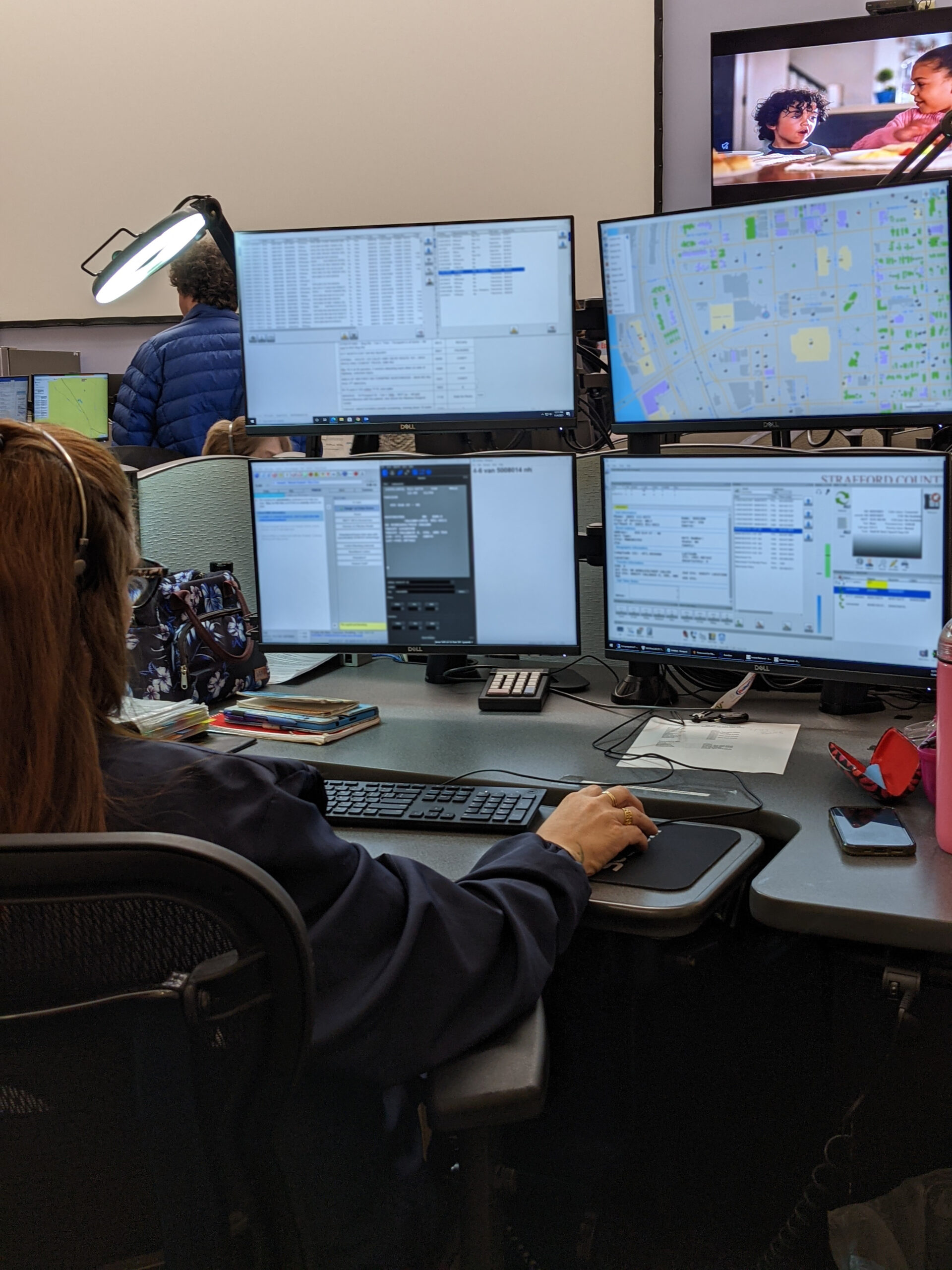
With the widespread network outage, the City of Dallas reported that all of their 911 services remained operational. All 911 calls were still being delivered to the emergency communication center (ECC) and sent off for dispatch. However, their computer-aided dispatch system was taken offline, so calls were manually dispatched using radio and pen and paper. The police and fire departments, according to one statement, are “flying blind”
Other city services were also impacted. Dallas’ city website was down, including the City’s utility website, which allows residents to make payments.
A Heavy Week for Dallas
Personally, I can only imagine the stress the City of Dallas’ employees are under this week. The IT professionals and network administrators are scrambling to get their systems back online while taking steps to ensure that sensitive information on the community members they serve hasn’t been leaked to nefarious actors. The 911 telecommunicators and dispatchers, who face enough daily challenges as it is, aren’t able to use the tools that help make them effective at their job.
In a statement, the City said that the attack and resulting network outage hasn’t affected their ability to respond to emergencies. However, I know that these emergency responders are having to work twice as hard to do their jobs in the aftermath.
Putting On Cybersecurity Armor
Cyber attacks against public agencies continue to happen, and at increasing rates as systems become more networked and digital information becomes more valuable. Sean Scott, CTO of SecuLore, famously says,
It’s not IF you’ll be attacked, but WHEN.
There are three major things the public safety agencies can focus on to mitigate their risk of being affected by an attack, and lessen the impact once they’re under attack so that critical services can remain operational.
Eliminate Entry Points
The first area is focusing on eliminating entry points for attacks. These entry points are typically either devices or people who have access to the network. Any chink in the cybersecurity armor, if you will, can let in an attack.
People
With people, a common entry point for cybersecurity attacks is fishing. Typically, this looks like a fake email sent to an employee who has access to the network. If an employee engages with this fishing attempt, they open up a window for the attackers to get in. To mitigate this risk, agencies and companies must regularly train their employees on proper cybersecurity “hygiene,” or best practices. Additionally, agencies should have tight cybersecurity policies in place that keep out common threats. Common examples of these policies include:
Devices

Devices on the network and systems that leverage the network can open up a similar window to attackers. Camera systems, computer-aided dispatch systems, logging recorder systems, phone systems, etc. can all be a window to let attackers in.
Fox4 News Reported: “‘All the attacker has to do is find one loophole, whereas we’ve got to be 100% that there’s no such thing as 100% security yet,’ said Bhavani Thuraisingham, professor of computer science at UTD and director of the Cybersecurity Research Institute at UTD.”
For this reason, it’s critical that every device and system be vetted for cybersecurity precautions. Some things to consider when purchasing devices or systems:
Early Detection
Because no network is 100% secure, it’s inevitable that agencies will suffer an attack. However, early detection is critical to reducing the impacts, fiscal and otherwise, of the attack. Once detected, agencies can quickly spring into action. The City of Dallas has implemented their own Security Operation Center (SOC) which monitors all cyber/network activity to detect strange activity which might indicate an attack. Their SOC detected the attack before it took down the network. Larger agencies and companies typically have their own SOC. For smaller agencies with less IT power, however, this can be difficult to do.
Companies like SecuLore offer SOC solutions geared towards these smaller agencies. These agencies can leverage SecuLore’s SOC services to detect threats early, without hiring a team of network experts and investing in a bunch of new technology. SecuLore, and companies that offer similar services, can leverage economies of scale to offer these solutions at a fraction of the price that a small agency would pay to implement their own SOC.
Prepared Action
Cyber incident response planning and training is critical to isolating the effects of an attack before it takes down critical systems. Without a proper response plan and the confidence to carry it out, agencies who detect a threat early have no chance of stopping it. There are a variety of cybersecurity consultants in the market now who specialize in public safety infrastructure. These types of companies, or any IT personnel with enough cybersecurity training and experience, can help agencies come up with a thorough and effective incident response plan.
Pieces to consider:
Email Me Articles Like This
Contents
- Cybersecurity for 911 Recording Systems: Building a Cyber-Strong Public Safety Recorder
1,398 Views
- AI in 911: Enhancing 911 & Dispatch While Ensuring Safety & Control
527 Views
- Strengthening Cybersecurity in 911 Centers: The Role of Strong Passwords and MFA During Cybersecurity Awareness Month
448 Views